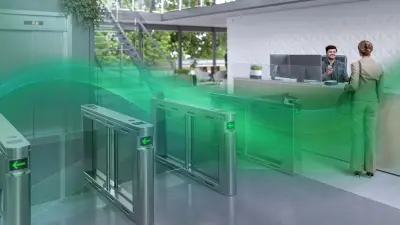
Biometric Access Control

Biometric access control can be used to enhance the security systems of a building or facility by adding an extra layer of verification. Unlike regular access control systems that use access cards and/or codes, a biometric access control system uses a person’s physical traits such as their fingerprints, face, palm veins and iris. These traits cannot be copied, thus improving the accuracy of identification and authentication. Next to this, biometric access control also offers the option of touchless access control.
FAQ
Any location that requires a high level of security, can implement biometrics for access control. The biometric security systems can be deployed at any site, be it indoors or outdoors. Bosch offers biometric readers that are used in a great variety of industries like: governmental buildings (including military), power plants, oil and gas facilities, commercial buildings, university campuses, prisons, data centers, airports, or warehouses.
Biometric-based access control systems are very secure thanks to the advanced technologies used in the readers. The biometric algorithms incorporated make the readers capable of coping with face changes (change of hairstyle, glasses, helmet, etc.) or different finger conditions (wet, dry, damaged). Our biometric readers also passed stringent cybersecurity penetration tests to ensure that hackers would not be able to get access to the software and steal data or inject malware.
When a user’s face or fingerprint is scanned by the biometric reader, a template is generated and compared to all the biometric templates contained in the reader or in the RFID access card. If there is a match, then entry can be granted.
Bosch access systems store the biometric data directly in the reader’s memory or on a server installed in the building.
All the documentations and installation guides for our biometric readers can be found in our product catalog.
Biometric security is used because you need it to protect your premises (i.e. your company assets and your employees) due to the nature of your activities. Therefore, costs related to such deployments have to be seen in the scope of reducing the risks linked to intrusions, acknowledging that using simple RFID cards may not be secure enough since they can be easily copied or at least stolen. This cannot happen with biometrics that by definition cannot be stolen.
Most privacy regulations mandate at least to inform users about the collection, processing and storage of their biometric data. It is also required to collect the user’s explicit consent for this and subsequent use with the readers, and there must be the possibility to opt out at any time. Additionally, more strict regulations like GDPR mandate that companies deploying biometrics document their deployment project in detail to ensure the biometric access control system is compliant with the regulations.
Criminals can attempt to use stolen data from a genuine user to fool the readers and get access to sensitive areas. This can be attempted using a photo found on the intranet, presented to the facial recognition reader camera, or by using thin wax membranes applied onto the fingers to try to fool the fingerprint sensors. Bosch has biometric readers that succeeded stringent anti-spoofing evaluations, such as the Presentation Attack Detection (PAD) one performed by reputed US laboratory iBeta.
Most biometric algorithms used nowadays are very accurate and manage to lower the level of false rejects (blocking access to an authorized person) and false acceptance (mistakenly accepting an unauthorized person). State-of-the-art fingerprint readers can manage all kinds of finger conditions (wet, dry, damaged or covered with substances like mud or oil) while the best facial recognition readers work efficiently with users of all heights (including wheel chaired people), in all light conditions, manage face changes (new hair color or haircut, hat, glasses) and also sanitary face masks (checking if a face mask is worn).
Yes, it is possible to combine an existing access system with biometric devices like fingerprint scanners, touchless readers and facial recognition readers. However, your system needs to support a suitable credential technology (i.e. MIFARE Desfire or iClass).